Three surfaces, one brain.
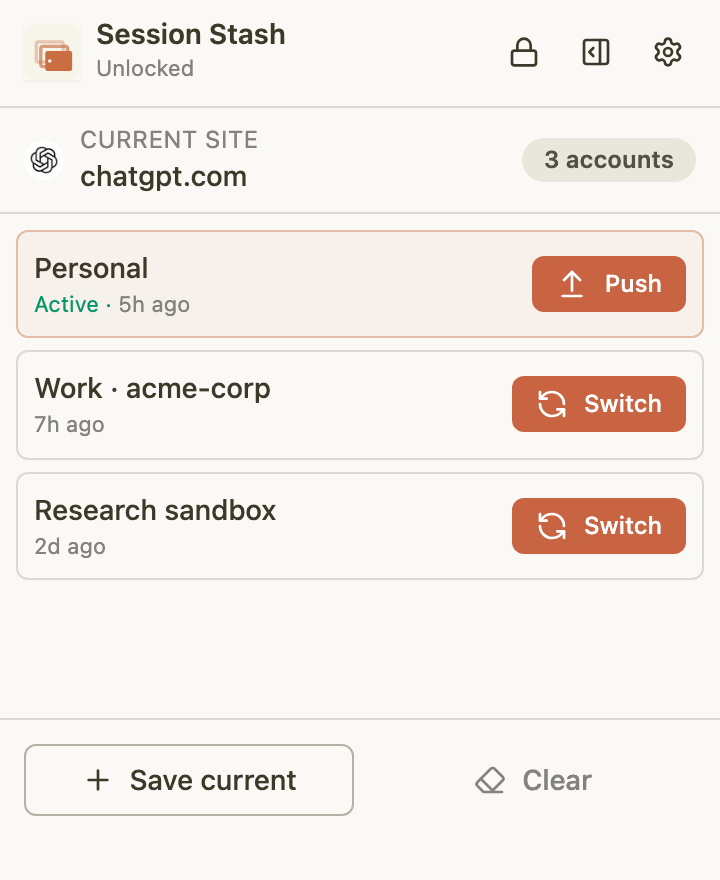
What you reach for.
The quick-switcher. Open with ⌥⇧S, pick an account, hit enter. Closes itself. Meant to feel like a keyboard shortcut, not an app.
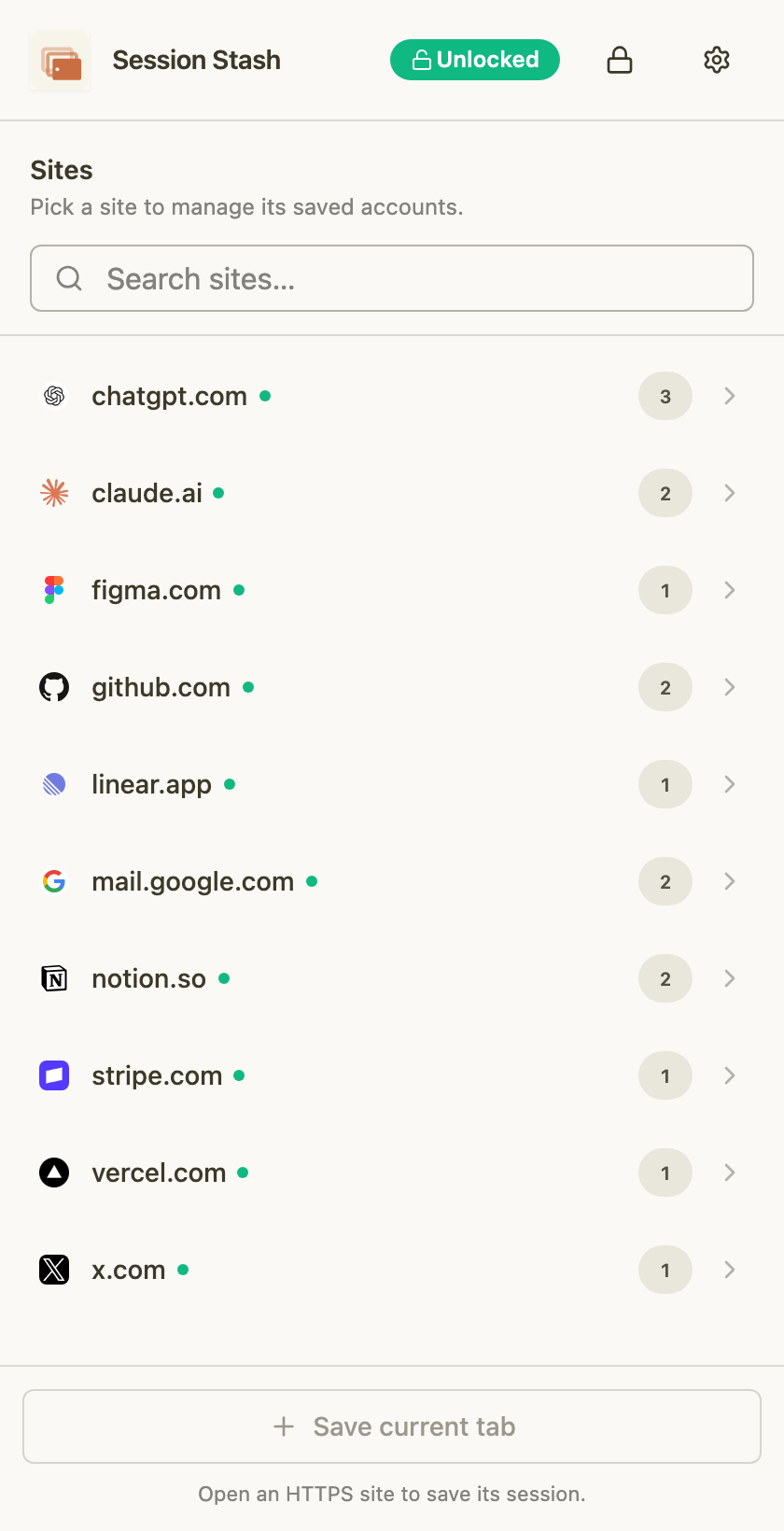
What you browse with.
A column anchored to your window, drill-in from site to account. Rename, delete, mark the active one with a green dot. One drawer per origin; github.com and chatgpt.com never mix.
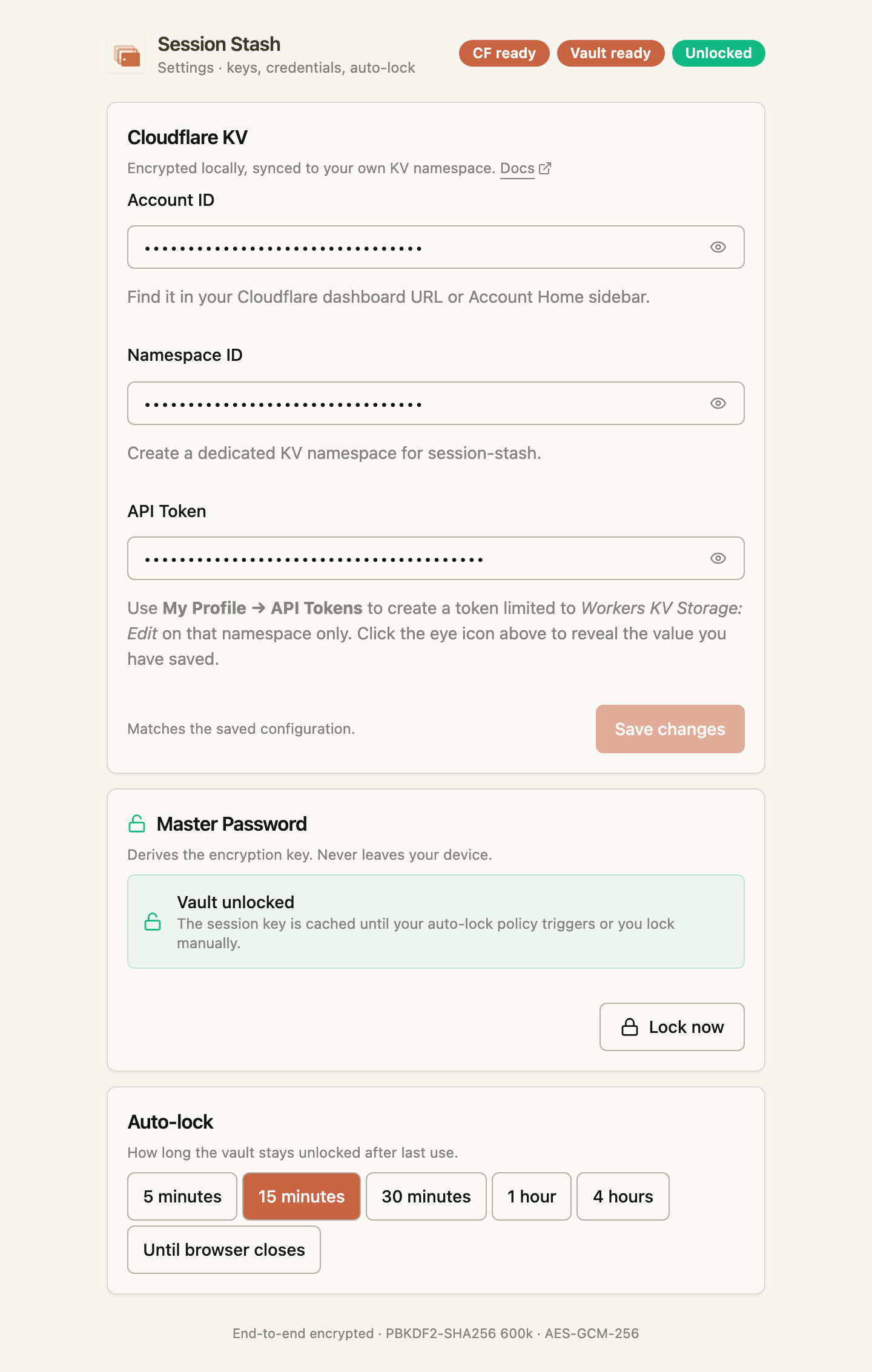
What you set once.
Your Cloudflare account ID, KV namespace, scoped API token, auto-lock interval, theme. The only surface that touches network configuration.